ACAD/Medre.A Worm Uncovered: Steals AutoCAD Design Files From Peru and Other Countries, Sends Them To China
Security watchers have discovered ACAD/Medre.A worm that specially targets design files created in the popular computer-aided design (CAD) software AutoCAD.
Security researchers recently uncovered high-profile, high-tech malicious code like Stuxnet, Duqu and Flamer, which were suspected to be part of a government-led espionage campaign. After tens of thousands of AutoCAD design files (blueprints) swiped using the ACAD/Medre.A worm, ESET (the antivirus firm) suspects the malware to have been designed for industrial espionage.
“ACAD/Medre.A represents a serious case of suspected industrial espionage. Every new design is sent automatically to the operator of this malware. Needless to say this can cost the legitimate owner of the intellectual property a lot of money as the cybercriminals have access to the designs even before they go into production. They may even have the guts to apply for patents on the product before the inventor has registered it at the patent office,” says ESET Senior Research Fellow Righard Zwienenberg.
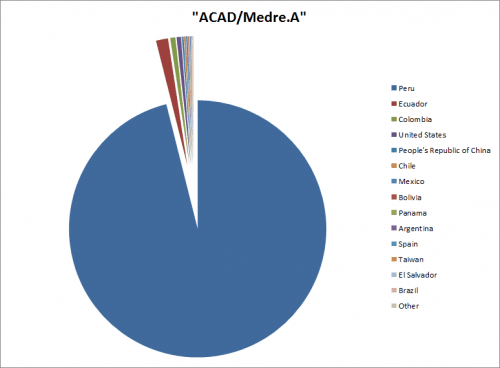
ACAD-Medre.A Pie-Chart (Image Source)
What exactly is ACAD/Medre.A doing?
According to ESET ThreatBlog, the ACAD/Medre.A worm has stolen tens and thousands of blueprints and have sent them via e-mail to a recipient. The worm tries to send the files to one of 22 accounts at 163.com and 21 accounts at qq.com, both Chinese free email provider. Mostly countries in South America were found to be mostly infected by the AutoCAD worm, Peru being the main victim of the attack. Even though, the miscreants were using China as dropsites in the delivery chain and were using Chinese internet resources but it doesn’t necessarily follow that they were Chinese.
ESET said they worked with Autodesk (the creator of AutoCAD software), Chinese ISP Tencent’s Desktop Security Business Division and CVERC, the Chinese National Computer Virus Emergency Response Center, to block email accounts associated with relaying of stolen AutoCAD drawings (blueprints).
How does ACAD/Medre.A infect the system and spreads around?
“The ACAD/Medre.A worm is downloaded to the system as a hidden file named acad.fas, usually accompanying a .dwg file (AutoCAD drawing). Once this drawing is opened, AutoCAD’s automatic loading routine calls the acad.fas file – present in the same folder – thus executing the malware itself. It tries to copy itself to several locations and alters AutoCAD’s automatic loading routine to make sure that it will be executed when an AutoCAD drawing (.dwg) is opened on the infected system,” said ESET.
“In addition to this, there’s a reason the script (even when already running on an infected system) is copied to the directory of the currently opened DWG. If the user wants to send his drawings to someone else, it is likely that he will add the directory into an archive and send the worm along with it,” added ESET.
The sample is able to infect AutoCAD versions 14.0 to 19.2 (AutoCAD 2000 to AutoCAD 2015) by modifying the corresponding native startup file of AutoLISP (acad.lsp). ESET found that even future versions of AutoCAD that will be released in 2013, 2014 and 2015, were supported by the ACAD/Medre.A worm.
How to identify if your system is infected by the AutoCAD worm, ACAD/Medre.A?
ESET has given a simple way to find if your system is infected by the ACAD/Medre.A worm. While simply the presence of a file name is rarely a fool-proof indicator of an infection, but the presence of files named “acad.fas” and “cad.fas” in the same directory as your .dwg drawings (especially if they’re found in multiple such directories) is a good indicator of the infection. Furthermore, if such files are marked as “hidden”, it’s almost completely clear that the computer is infected.
If you are interested in going through the technical details of the ACAD/Medre.A worm, you can read here.
How to clean your system from ACAD/Medre.A worm infection?
You can use the free stand-alone ACAD/Medre.A worm cleaner by ESET to clean your system. You can also use the free ESET Online Scanner to clean your system. If your system is not protected by an antivirus you should get one now.
With all these high-profile malware uncovered now-a-days, which were mostly suspected to be a part of government-led or industrial espionage campaign, how safe are we today? What’s your take on these uncovered malware? Share your thoughts with us through comments below.