Microsoft Fixes Internet Explorer Vulnerability (Security Advisory 2963983)
Microsoft has issued an out-of-cycle security update for Internet Explorer vulnerability (Security Advisory 2963983) uncovered on Saturday, April 26, 2014. Microsoft even issued the fix for Windows XP (which is now no longer supported by the company), running Internet Explorer. This vulnerability was so severe in nature that IE users were asked to use an alternative browser for the time being until an official fix is issued. The US and UK even issued warnings about using Microsoft Internet Explorer web browser.
The security update for the Internet Explorer vulnerability was delivered at 10 a.m. Thursday, May 1, 2014. The security issue affected all versions of Internet Explorer, starting of the age-old Internet Explorer 6 through the latest version Internet Explorer 11. The vulnerability could allow remote code execution if a user views a specially crafted webpage using an affected version of Internet Explorer. After successfully exploited, the attacker could gain the same user rights as the current user. If the current user has fewer rights the impact will be less in comparison to users who have administrative user rights.

The bug was first found by the security firm FireEye Inc. and was reported to Microsoft. The company also updated the Security Advisory 2963983 page stating that it has completed the investigation into a public report of the vulnerability. The company has issued Microsoft Security Bulletin MS14-021 (critical) to address the issue. The vulnerability addressed is the Internet Explorer Memory Corruption Vulnerability (CVE-2014-1776).
At the company’s official Microsoft Security Response Center, Dustin C. Childs, Group Manager, Response Communications of Microsoft Trustworthy Computing said “At approximately 10 a.m. PDT, we will release an out-of-band security update to address the issue affecting Internet Explorer (IE) that was first discussed in Security Advisory 2963983. This update is fully tested and ready for release for all affected versions of the browser.” He further said, “The majority of customers have automatic updates enabled and will not need to take any action because protections will be downloaded and installed automatically. If you’re unsure if you have automatic updates, or you haven’t enabled Automatic Update, now is the time. For those manually updating, we strongly encourage you to apply this update as quickly as possible following the directions in the released security bulletin.”
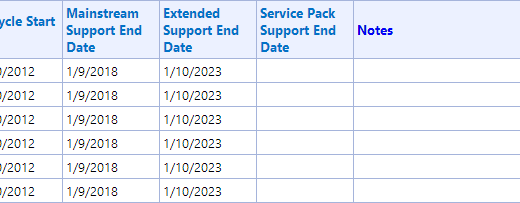
Users who are still on Windows XP must be aware that the operating system is no longer supported by Microsoft. Although to fix the issue, an update was also made available for Windows XP, Childs asked users to upgrade to Windows 7 or Windows 8.1. Childs said, “we have made the decision to issue a security update for Windows XP users,” noting that “Windows XP is no longer supported by Microsoft” and the Redmond software giant “encourage customers to migrate to a modern operating system, such as Windows 7 or 8.1. Additionally, customers are encouraged to upgrade to the latest version of Internet Explorer, IE 11.”
Similar Articles
Source: Microsoft Security Bulletin MS14-021 – Critical